A Fox News investigation has now revealed that on November 8th, a coordinated attack netted $9 million using cloned cards in 49 cities, worldwide. The attack occurred all over the United States, Montreal, Moscow, and Hong Kong in about 30 minutes.
Another scary aspect to this attack was that the hacker was able to remove the daily withdrawal limits of the cloned cards. According to the Washington Post, 100 cards were used and fake deposits were used to refuel the balance on the cards. Large withdrawals were then made again and again on the cloned cards. Please note this represents that a very small percentage of the total cards compromised were used in scheme. No information was available on how they refueled the accounts.
I've seen accounts refueled using bogus checks, however in this instance, I would suspect it occurred in a more electronic manner. This leads me to believe we will see more disclosures regarding this case as time goes on.
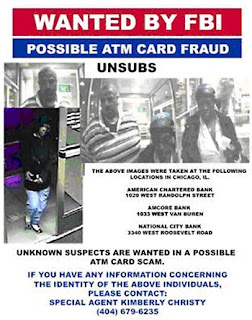
According to official reports, there are no primary suspects in the case. Photographs of some of "lower level soldiers" used to withdraw the money have been released in the hope that (if caught) they will provide information on the people, who provided them with the cloned cards. Unfortunately, with the anonymous nature of the Internet, coupled with the fact that chat-rooms are often used to facilitate the distribution of stolen data, the lower level soldiers might not know the identities of the main players, themselves.
In the recent Heartland breach, it was disclosed that they met PCI DSS (Payment Card Industry Data Security Standards). According to Visa's list of PCI DSS certified vendors, "RBS Lynk" (Royal Bank of Scotland) is certified. PCI DSS standards are the payment card industry's solution to protecting their data from being misused.
I also discovered that RBS World Pay and TrustWave put out a press release in 2007 announcing they were providing level 3 and level 4 merchants with a specialized data security service to identify their risks and vulnerabilities. The idea behind this service is to help these merchants become PCI DSS compliant.
Interestingly enough, TrustWave also certified Heartland in 2008, according to the article I read in Dark Reading.
PCI DSS has been criticized as being expensive for merchants and now we are seeing it compromised, too. The sad thing is that despite a lot of money being shelled out to become PCI DSS compliant, the people shelling it out seem to be just as vulnerable as they were before. In fact, someone might conclude that PCI DSS is giving everyone a faux sense of security (opinion).
As usual, in these cases, a class action law suit has been filed against RBS WorldPay. WorldPay has also announced the cardholders will not be held liable for the charges, according to the page on their site about this matter.
Thus far, according to all the sources I read, no identity theft has occurred. My guess is that because the 1.1 million people compromised are monitoring their credit, none will occur in the short-term. In most of the many breaches I've read about, very little of the information was used after the breach was disclosed. If you think about it, this makes sense because measures have been taken to make the information useless to criminals.
To close, I would like to add another thought. The fact that payroll information — which included personal information — was hacked might point to another example of how storing too much personal information in too many places is the root cause of the problem.
There has been a push to put everything from payroll to government benefits on payment cards. When this occurs, personal information as well as the financial data used to produce the debit card accounts is stored to process the transactions. Since employers (and the government) use vendors (card issuers) to accomplish this task, this means we have sensitive information being transferred to third parties. It wouldn't surprise me if these third parties transfer the information somewhere else when they outsource it, all over again.
Perhaps, what is needed is a common sense solution to the problem. As long as we keep sending information all over the place, it creates too many points where it can be compromised. The bottom line to all this is we appear to be making it too easy for criminals to take advantage of the situation.
The costs are getting out of control, too. Although I've never seen any information on how much of this is going on, the Washington Post quoted a source from the security industry (Ori Eisen, 41st Parameter) as stating $50 million was lost in one month in New York City alone last year.
I wonder if any of our bail-out (taxpayer) money is being used to cover these losses. Although, I can't say for sure, the people it was given to can't seem to say where it has gone, either. Granted, it might be a long shot, but the money had to be given to cover losses caused by people who were a little too greedy in the first place. We need to wake up and realize that there is no free lunch and the costs of all these types of scenarios are passed to all of us when history is written.
There is no such thing as zero fraud liability!

2 comments:
I think PCI DSS and Penetration Testing are all important ! And thank you to give so good resources!
The PCI DSS standard requires that a penetration test be undergone annually or following a significant change to our network.
Post a Comment